Posts
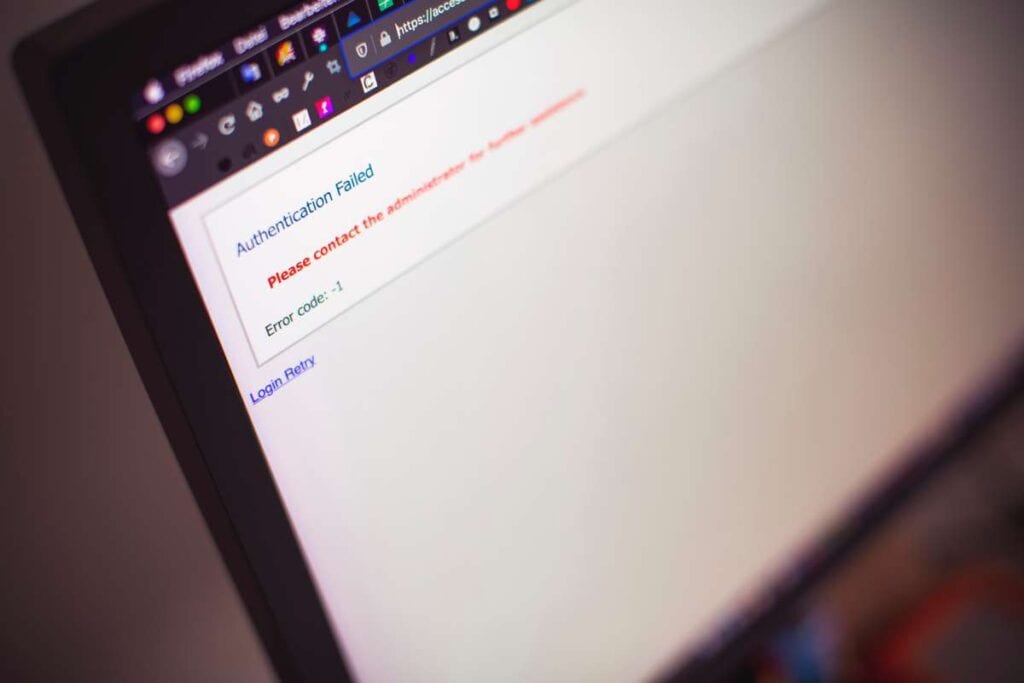
One way to put it is that authentication is the process of verifying the identity of a person seeking access to a resource. A username or password were sufficient for […]
Read More →Many once manual tasks now have digital analogues, allowing us to keep up with the rapid speed of today’s digital environment. Therefore, it is unthinkable today to go a whole […]
Read More →Biometric access control is a modern security system that relies heavily on scientific research and technological innovation. The great news is that everything can be explained in a simple way. […]
Read More →I’m confused about the distinction between RFID and QR code asset tags. The two are interchangeable and serve similar functions. In contrast to the QR code, which requires repeated scanning […]
Read More →Password breaches are the most common type of cloud account breach, accounting for 77% of all breaches. Even when firms make it clear that employees must develop secure passphrase practises, […]
Read More →There are some common sense things to keep in mind whether or not a facility already has a physical security plan in place. Managers of single or multiple buildings can […]
Read More →Do you want to upgrade the security of your commercial building by installing an access control system? Do you wish that you could manage who enters your building and at […]
Read More →When a company produces, designs, or develops a product, it creates intellectual property that may be licenced or sold to other businesses or individuals. Organizations must ensure the well-being of […]
Read More →Data centres are typically located in generic buildings with minimal or no exterior marking to prevent snooping. The intangible assets protected here include, but are not limited to, private and/or […]
Read More →If you’re a desk jockey who spends hours at a computer every day, you know how easy it is to get sidetracked by things like browsing the web for deals, […]
Read More →