Posts
When it comes to stopping unauthorised entry, knowledge is power, and that’s especially true when it comes to understanding the various forms it can take and how to stop each […]
Read More →If you’ve been living out of a tech office or coworking space for any length of time, or if you’ve hopped around from company to company, your wallet is probably […]
Read More →In financial institutions, the users logging in are working with other people’s money and sensitive personal information, making authentication, the process of identifying if an individual is who people say […]
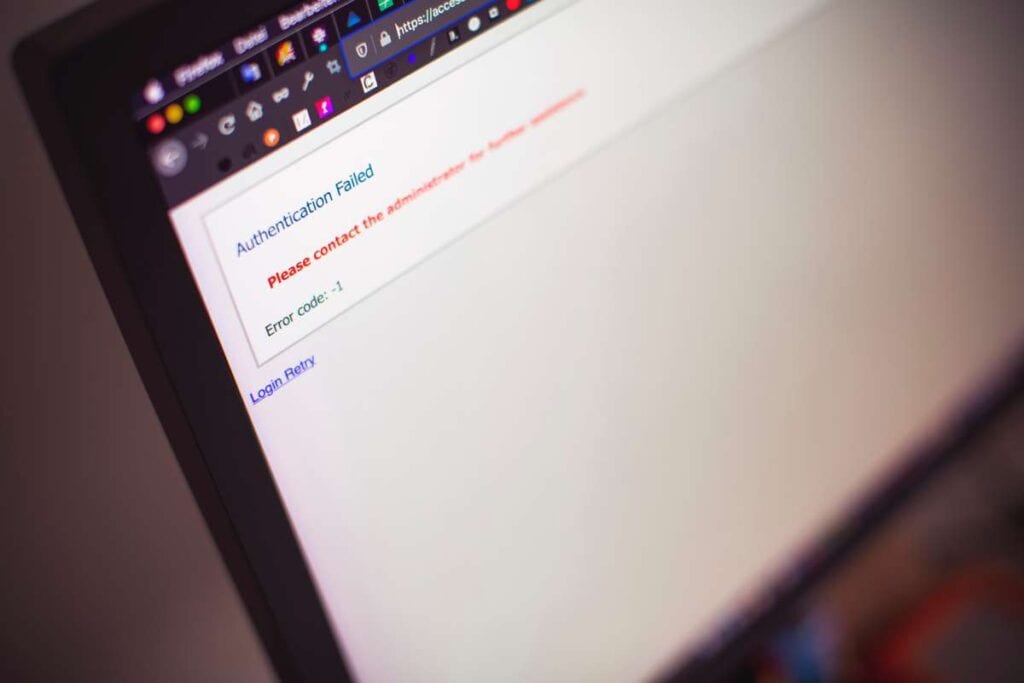
Read More →Authentication refers to the steps used to ensure that a user or device is who they claim to be online. Logging into a website typically involves providing a user name […]
Read More →Credentials are being used together (and, frequently, interchangeably) as businesses develop their digital maturity in this age of secure cloud-based systems and rigorous of online safety. Despite their superficial similarities, […]
Read More →Authentication is used by a wide variety of applications to grant customers access to a service, whether for work or for personal usage. Varying verification methods are needed, each corresponding […]
Read More →Protection at the physical layer is the foundation of any other security measures taken. There may be less dire consequences from a breach of lower-level security procedures, but losing physical […]
Read More →There have been security risks, in varying forms, since the beginning of time. There will always be a vantage point from which you monitor a potentially dangerous situation. Padlocks have […]
Read More →There are a variety of mechanisms for controlling who is allowed to enter a building or other area of physical property. To rephrase, physical access control serves to restrict access […]
Read More →Similar to the wireless clickers that come with some automobiles, an access code fob is a handheld remote control device. They both serve the same purpose. Your vehicle’s wireless remote […]
Read More →