There are a variety of mechanisms for controlling who is allowed to enter a building or other area of physical property. To rephrase, physical access control serves to restrict access to just those who have been granted permission to do so.
A security door, a gate, or a fence are all examples of physical access obstacles, but there are other barriers of authority that can be just as difficult to overcome.
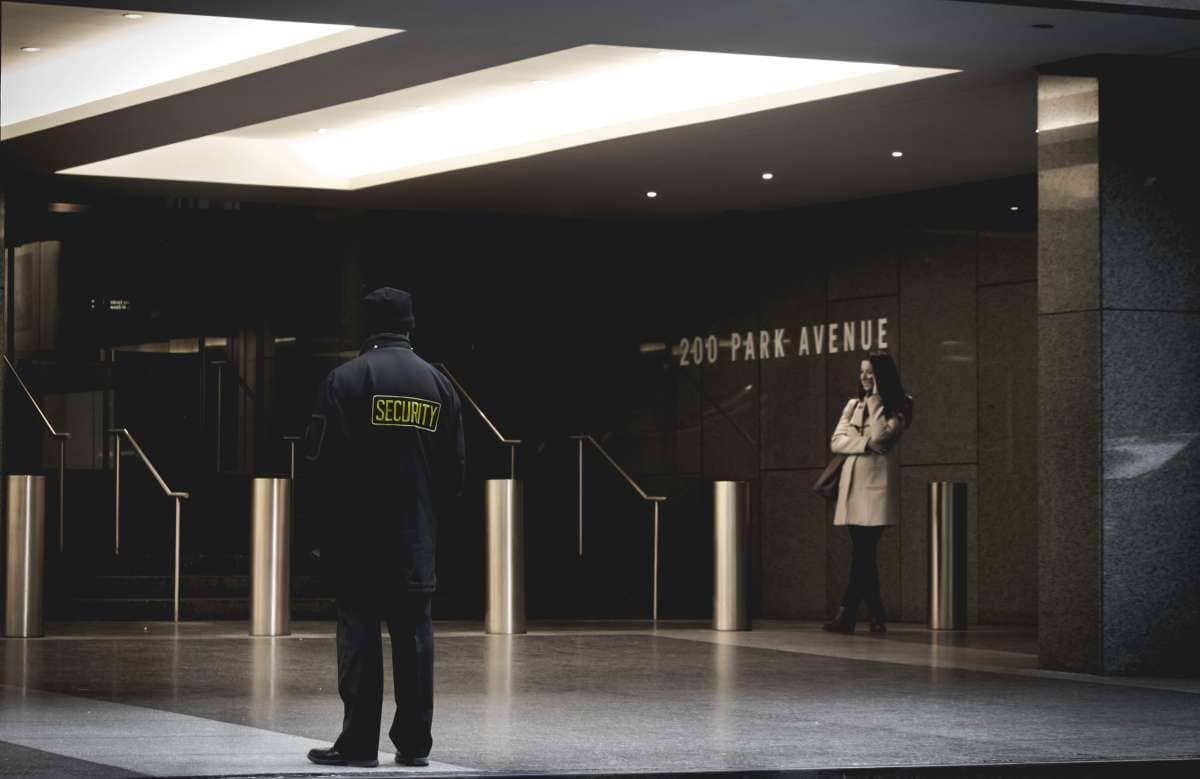
A management barrier could be a human or a signpost outlining the rules. To illustrate, consider a restaurant with a sign that reads, "Only employees beyond this point," or a hospital receptionist who admits guests during and outside of visiting hours.
The term "physical access control" generally refers to a set of barriers, which, along with "authority barriers" and "authorisation plans," allow only authorised individuals in while keeping everyone else out.
Controlling who can enter a building is as vital to security as enforcing a strong password policy.
Whereas cyber security is concerned with safeguarding data that can be exploited to harm an organization's or an individual's credibility, money, or productivity, physical security is concerned with safeguarding actual people and tangible assets.
The tragic results of a violent person entering a job with a weapon are frequently reported on the nightly news.
Physical barriers are an alternative to more extreme measures like locking the doors to data centers or other areas containing potentially dangerous products and equipment.
Theoretically, anything from natural calamities to industrial espionage to terrorist attacks on workers. Can you handle this as a company? Just picture it: it's 2 in the morning and there's no one around just to listen to the sound of shattered glass and hasty footfalls.
The first worker returns to work the following day and immediately contacts law enforcement upon seeing the chaos.
The vandalism, as reported by the police, occurred for no apparent reason. And then, two weeks later, the president calls a meeting because the local press is covering your item and has just reported that the project has run thousands of dollars over budget.
The vandalism was actually an effort of industrial espionage. The hacker had broken into the system via a bootable Linux distribution and stolen the victim company's data.
Having proper protocols in place could have helped avoid this problem. In reality, system takeover may be accomplished in a matter of seconds by anyone with direct access to a computer.
Go over basic physical security measures to implement suitable access controls and reduce the likelihood of an attack. There are three facets to any form of access control: the physical, the administrative, and the technology.
FREQUENTLY ASKED QUESTIONS
Common physical access control examples of access points include security gate systems, turnstiles and door locks. A secure space can have a single access point, like an office inside a larger complex, or many access points.
Physical control is the implementation of security measures in a defined structure used to deter or prevent unauthorized access to sensitive material. Examples of physical controls are: Closed-circuit surveillance cameras. Motion or thermal alarm systems.
Physical access control is an electronic system allowing organisations to restrict and regulate who can gain entry to different locations or assets. It's a way of identifying users and employees, authenticating who they are through different methods and authorising them access to items or areas.
Key locks are the most common and inexpensive form of physical access control device. Lighting, security guards, and fences are all much more cost intensive.
There are two types of access control: physical and logical. Physical access control limits access to campuses, buildings, rooms and physical IT assets. Logical access control limits connections to computer networks, system files and data.
Plan For Safety In The Real World
Information, buildings, persons, equipment, and other material wealth are what physical security is primarily concerned with safeguarding. Furthermore, physical security addresses concerns that arise before crimes, sabotage, and terrorist attacks occur. What potential causes have the highest potential to become immediate dangers?
- Issues with personnel: firings, walkouts, and illnesses.
- Vandalism and sabotage.
- Broken hardware.
- Tornados, earthquakes, storms, and tidal waves are all examples of natural catastrophes.
- Terrorism, arson, and bombing are examples of man-made disasters.
- Disruption to the supply of food, water, and energy.
The first step in figuring out how to best safeguard yourself is identifying the specific dangers you face.
It's important to have a secondary phone system and a generator to keep essential functions running in the event of an outage, such as keeping the lights on and keeping staff safe.
Having a well-thought-out service contract and certain replacement parts on hand can come in handy in the event of a hardware failure.
In particular, it is wise to study the regulations governing workplace safety in the nation in which your business operates.
To restrict entry to unauthorised individuals and reduce the possibility of harm being done, you msut have physical access restrictions.
A simple fit just on a door lock, for instance, can deter many would-be burglars. Even the most dogged invader can be deterred by the presence of fingerprint scanners, including such iris scan or fingerprint recognition.
A means to buy time to alert the proper authorities is sometimes all that's needed to fix the problem. However, the door isn't the only thing that needs to be shut.
It may be necessary to restrict access to mobile devices, workstations, and servers. You may have no idea when an intruder sneaks into the facility, steals a computer, and leaves without anyone noticing. Sadly, this sort of thing frequently occurs.
As the prevalence of USB, COM, and LPT theft rises, more and more businesses are taking the preventative measure of trying to remove all drives from employee computers and enforcing additional BIOS secure passwords to stop workers from installing personal apps, trying to gain unauthorised access, and eventually taking part in the robbery.
Using the terminal server in tandem with a bootable Linux system is one option for increasing safety. Since DHCP is also not included, issues with spyware, malware, and viruses are usually avoided.
The use of electromagnetic waves to intercept systems, decode data, and replicate it in an untraceable location presents another security difficulty.
Shielded computer enclosures can save you a lot of trouble if you use the right kind of special building materials and absorption materials.
Building security is also essential. The best plan of action is to staff the reception area with people who have received proper training in protection and security.
Building construction is beyond the scope of this article, but suffice it to say that biosensors, motion detectors, and sirens when barriers are penetrated are absolute necessities.
Moreover, installing tall moving led lighting that will react to any effort to breach its walls appears to be a great alternative. If an intruder scales a wall or fence, a focused light beam will shine directly into their eyes, illuminating only their silhouette.
It is important to keep in mind that even the most sophisticated security system can be compromised by human error. Furthermore, studies suggest that the most prevalent attacks were internal attacks conducted by unhappy or even irate personnel.
That's why it's crucial to invest in staff training that prepares them to respond effectively in a crisis, whether caused by natural disasters or by a deliberately orchestrated attack on technology.
This sort of training shouldn't be an annual event, but rather something done once every three months. Theoretical understanding is important, but so is having some hands-on experience.
Scenarios in which participants take on the roles of real-life figures to represent real-world circumstances can be instructive. Inspections of employees should be seen as a preventative action by all businesses.
It's smart to verify a candidate's background before extending an offer of employment, including looking into whether or not they have a criminal record or are wanted by authorities.
As a matter of fact, this is how you'll find out if an employee poses any kind of future risk.
In addition, you may receive information about upcoming shifts or job swaps during private, one-on-one interviews with staff members. Consistent communication will eliminate unethical behaviour and accidental damage.
An ex-employee should be escorted off the premises as soon as they have returned all corporate property. The former worker's effort at sabotage will be foiled if this happens.
Having access to tv security systems and backup power sources is of utmost importance.
There is no question that if burglars try to get into the business, they will be able to be identified and their movements recorded by the company's surveillance cameras. Motion detectors and heat detectors are standard on some systems.
After being triggered, these detectors will send out an alarm. There are a wide variety of additional advantages to putting in a high-quality CCTV system.
In addition, the possibility of hardware failure should be taken into account. This is the most likely outcome. So rather than wondering if a part will fail, you should rather wonder when it will.
When designing their products, many component manufacturers simply think about how long it will take to fix something and how often it will break. However, a system backup is also an essential component. Any data copies made should be kept in at minimum two locations, since this will provide redundancy and safety in the case of a catastrophe or system failure.
Data vaulting involves the compression, encryption, and storing of sensitive information in a geographically separate, highly secure location. All insurance and safety plans necessitate this method.
Let's get to the juice. You need to make sure that, in addition to the concealed electrical wiring, there is a reliable power supply.
By doing so, you can avoid problems caused by a lack of energy (such breakdowns and voltage spikes), or an abundance of it (low voltage or current, no power). UPS systems are useful for this purpose. Damage to electrical components, loss of data, and improper network connections are all possible results of using energy that is not properly regulated.
As a matter of course, you are not concentrating solely on the power generated by the plant.
Wind turbines, solar panels, backup power for collecting extra energy, and other power sources like diesel generators can all be installed in addition to the normal connection from the power plant.
It's important to remember that the computer system is likewise governed by the power law: a value of 0 indicates the absence of a pulse, and consequently, no vibration is produced. An electric circuit is the outcome of a group of connected computers.
By convention, a voltage reading of 0 volts is represented by the number 0, whereas a reading of 3 to 5 volts is shown by the format 111 001, which indicates the following tension: 3,3,3,0,0,3. The transmission of signals should be unimpeded under ideal conditions.
Therefore, it is crucial to have a good grounding system in place so that any excess energy may be dissipated. Regular breakdowns are the result of voltage spikes, which can be avoided with proper grounding.
A ground wire that has been properly put offers low enough resistance and large enough capacity to shield the system before a dangerous voltage level emerges. It's not uncommon for the grounding wires to stop functioning if even one outlet has a broken cord or bulb that's been screwed in incorrectly.
In extreme cases, the entire structure may require numerous grounds, which is a significant challenge due to the inherent inequity in the electromotive force of the various circuits.
Another major concern is the emergence of an electrical circuit in a standalone computer network with a grounded network. In addition, remember that the positive charge system always has current flow from the negative charge. Network outages, corrupted data, and even physical damage to hardware could all result from such a disruption to the digital signal.
Choosing The Right Physical Access Control
The evolution of security technology has resulted in the availability of more flexible and feature-rich physical access control systems.
When deciding how much money to allocate towards a physical control system, one option to consider is the credentials that will be issued to users.
Keycards first appear to be the best option if you are making your credential choices on a tighter budget. But given how often keycards are misplaced, they can add up to more money in the long run.
In addition, a missing keycard can be a security risk if it falls into the wrong hands. For further security, consider using two-factor authentication or purchasing encrypted keycards if your company still has to use keycards or fobs.
Accessing the building via a mobile credential, which includes multi-factor biometric authentication, is the most secure and convenient option for your consumers. Phones are much less likely to become forgotten at home, or handed around the office, which means you won't have to replace as many keycards.
System administration and upkeep should also be factored into your plans for physical access control. The readers and local servers of many older access control systems are inconvenient and must be managed and updated manually.
If you're using an older reader, you should upgrade it as soon as possible because of the increased vulnerability it has to tampering, and because of the delay in updating your system.
Furthermore, an admin will likely be required to be present if privileges need to be transferred or established. Consider methods that employ more up-to-date software if you foresee needing remote access to your computer or if you require the latest security upgrades in real-time.
The use of a cloud-based physical system for access control (PACS) has many advantages over traditional on-premises solutions.
Systematic Explanation Of a Physically-Based Access Control Procedure
- Industry-leading Proprietary Triple Lock technology to ensure 99.9% uptime.
- Use a keyless entry system Methods such as "Wave to Unlock," "Apple Watch," "NFC" and "RFID" key card & fobs, and "mobile" and "tablet"
- Credentials and a digital Guest Pass are instantly accessible via mobile device.
- With an open API, you may connect as many applications and enterprise resources as you like.
- A centralised cloud-based interface for managing all entries and locations remotely.
- Conveniently fits any door density with conventional wiring and tamper-proof hardware
- Automatic upgrades and full-disk encryption make this hardware and software future-proof.
What Exactly Is Cloud-Based Physical Access Control?
This PACS allows for a more adaptable and scalable security solution by connecting your user access hardware (readers, hubs, and control boards) with software on the cloud. Some advantages of a cloud-based PACS include:
- The ability to trigger, unlock, and lock down hardware remotely.
- New user credentials are issued instantly, and access can be immediately revoked if necessary.
the capacity to receive alerts instantly upon the occurrence of access events or the detection of a security threat - Cloud-based maintenance and troubleshooting eliminates the need for onsite technicians.
- The latest security patches are acquired from the cloud and installed automatically.
- Access logs are kept in real-time and may be viewed from any external controller thanks to cloud storage.
- The potential for your building and building system for access control to work in tandem with various forms of antivirus software, like video monitoring, visitor tracking, communication apps, and space management tools.
Conceiving a Strategy For a Physical Security System
There are a few things to consider before beginning the process of installing a new physical policy for access control in your facility in order to ascertain whether or not the current system satisfies your demands and what may be missing.
- Where do you feel most vulnerable in terms of safety?
- To what extent would you need to ensure the safety of so many structures?
- Do you need to restrict entry to any outbuildings, such as parking garages?
- How many doorways/exits will require physical security checks?
- In what quantities would regular or occasional access be needed?
- Can you provide access to several departments and/or levels of employees?
- Which forms of identification are required?
- When it comes to your physical control system, are there any regulations that it must follow?
You should train all employees who will be using the wholly new access control system, including admins, IT providers, and home consumers, to utilise the system properly after installation.
When switching to a new physical access control system, you may decide to implement new policies, such as asking users to activate cell credentials via a new mobile app or turning in old badges in exchange for new encrypted credentials.
Both administrators, who will have to add and remove users' access, and end users, who will need to be shown how to use the new credentials, may require additional training.
After the new system is built, it will be useless unless the training program for physical access management procedures is provided. It will be easier on everyone if the new access control policies are shared with them in advance of their implementation.
Conclusion
Commonly, when people talk about "physical access control," they're referring to a series of checkpoints and gates that let in only those who are supposed to and keep out everyone else. A management barrier may take the form of either a person enforcer or a rule-posting structure.
Data centres and other places housing potentially hazardous materials and equipment can be further protected by installing physical barriers in addition to locking doors.
Review the fundamentals of physical security so that you can set up appropriate access restrictions and lessen the chance of an attack. Physical security, administrative procedures, and technological means all contribute to the overall success of an access control system.
The first step in figuring out how to protect oneself is to recognise the threats you face. Limiting who may use what on what mobile devices, computers, and servers could be important.
Using electromagnetic waves to intercept systems, decode data, and reproduce it in an untraceable place is another security risk.
Using the correct kind of specialised construction materials and absorption materials, shielded computer enclosures may spare you a great deal of headache. Companies should see personnel inspections as a preventative measure.
Once former workers have returned all company property, they should be removed out of the building. It is crucial to have backup power and security measures in place.
Every backup copy you make should be stored in two different places. In addition to the disguised electrical cabling, you must ensure that there is a steady supply of electricity. Back-up power supply units are helpful for this.
Alternate power sources, such as wind turbines, solar panels, battery banks, and so on, can be set up. Keep in mind that the power law is the underlying principle of the computer system.
Try utilising mobile credentials like "Wave to Unlock," "Apple Watch," "NFC," and "RFID" instead.
There are several benefits to using a PACS that is hosted in the cloud as opposed to a local server. A PACS is a cloud-based security solution that integrates access control hardware and software.
The ability to remotely activate, unlock, and lock down hardware is just one of the many benefits of a cloud-based PACS. Credentials for new users are provided promptly, and existing users' access may be cancelled just as quickly.
Changing to a different physical access control system gives you the opportunity to establish new norms.
Users may be required to activate cell credentials via a new mobile app or trade in outdated badges for secure identification cards. If everyone is aware of the new access control regulations ahead of time, it will make things much simpler.
Content Summary
- It is possible to restrict access to a building or other piece of real estate in a number of different ways.
- To restate, the purpose of physical access control is to limit entry to authorised individuals only.
- Physical barriers to entry may take the form of a locked door, gate, or fence, but the more insidious kind may be found in the form of arbitrary bureaucratic procedures and policies.
- A robust password policy is important, but access control is even more crucial.
- When it comes to protecting people and material possessions, physical security takes precedence over cyber security, which focuses on preventing unauthorised access to information that may be used to ruin someone's or a company's reputation, bank account, or output.
- The act of vandalism was essentially an attempt at corporate espionage.
- Review the fundamentals of physical security so that you can set up appropriate access restrictions and lessen the chance of an attack.
- Physical security, administrative procedures, and technological means all contribute to the overall success of an access control system.
- Physical security is concerned with protecting things like data, buildings, people, and equipment.
- Recognizing the threats you face is the first step in developing a defence strategy.
- Physical barriers are a must if you want to prevent unauthorised people from gaining admission and minimise the risk of an attack.
- Limiting who may use what on what mobile devices, computers, and servers could be important.
- One way to beef up security is to use the terminal server in combination with a Linux machine that can boot.
- Using the correct kind of specialised construction materials and absorption materials, shielded computer enclosures may spare you a great deal of headache.
- Safety in the building is also crucial.
- The most prudent course of action is to staff the front desk with individuals who have had extensive training in security and protection.
- Bear in mind that even the most cutting-edge security system might fall victim to human mistake.
- It is important to provide your personnel the training they need to handle any kind of crisis, whether it's the result of a natural disaster or a well-planned cyberattack.
- While a firm grasp of the fundamentals is essential, nothing beats getting your hands dirty.
- Real-life situations are often used as models in educational role-playing scenarios.
- Companies should see personnel inspections as a preventative measure.
- It's crucial to have both a working television security system and a reliable backup power supply.
- Some systems are equipped with standard motion and heat detectors.
- Besides the obvious security benefits, there is a long list of other reasons to invest in a top-notch CCTV system.
- The risk of hardware malfunction must also be considered.
- A backup of the entire system is equally crucial.
- If you're going to make a copy of your data, you should be sure to store it in two different places to ensure its protection in the event of a natural disaster or technical failure.
- In addition to the disguised electrical cabling, you must ensure that there is a steady supply of electricity.
- In order to disperse any surplus energy, a reliable grounding system is essential.
- Emergence of an electrical circuit in an untethered computer network is another significant issue.
- The cost of issuing user credentials is something to think about when allocating funds for a physical control system.
- The management and upkeep of the system should be considered alongside the physical security measures.
- Whether or not your building's access control system is compatible with other security software, such as video surveillance, visitor tracking, communication applications, and space management utilities.
- In order to determine whether or not the present system meets your expectations and what may be lacking, there are a few things to consider before commencing the process of establishing a new physical policy for access control in your business.
- After installing a brand-new access control system, it is imperative that all personnel utilising the system, including administrators, IT providers, and home users, receive adequate training on how to operate the system.
- Policy changes may be necessary when migrating to a new physical access control system. For example, you may require users to activate cell credentials using a mobile app or swap out their old badges for encrypted credentials.
- Additional training may be needed for both administrators, who must add and revoke users' access, and end users, who must be trained how to use the new credentials.
- Without a training programme for physical access control processes, the newly constructed system will be meaningless.
- If the new access control regulations are communicated to everyone in advance of their implementation, it will make everyone's lives much simpler.