Protection at the physical layer is the foundation of any other security measures taken. There may be less dire consequences from a breach of lower-level security procedures, but losing physical protection almost always leaves you wide open.
The usefulness of security protocols is often underestimated, despite the fact that they are expensive. Many security measures have the unintended consequence of decreasing the incentive for many businesses to adopt more stringent measures.
Although it's comforting to believe that your most trusted colleagues are also your most loyal allies, statistics reveal that attacks often come from within rather than without.
Putting in place physical safeguards need not always break the bank. Locks and other such items are inexpensive but effective deterrents and time-buyers against would-be burglars. Automatic logoffs, screensaver with password protection, and session controls can all be implemented at little to no cost.
For optimal physical safety, paper records management is also essential. To avoid being a victim of dumpster diving, simply invest in a shredder.
It's not a new phenomenon that people try to breach physical protections. They predated the conception of modern organisations and computer networks. An attacker can choose from a wide variety of methods.
Tools like lock pick kits, wiretap devices, and scanners are all within the reach of an intruder.
Attackers with even rudimentary computer knowledge can employ wireless keyloggers or purchase security equipment to disassemble and analyse. Security experts, in the end, must accept that the war they are a part of will go on indefinitely and that they aren't fighting a single battle.
The best offence is a strong defence, as the old adage goes. Get the upper hand on would-be thieves by installing a solid business security system.
You can feel safe knowing that your property is protected by an effective physical security system. However, investing in a surveillance system that offers many layers of physical security protection is the greatest line of defence.
You may feel safe knowing that your business's exterior and interior are both safeguarded by a reliable security system. Intricate layering will make it more difficult for hackers to obtain sensitive data.
FREQUENTLY ASKED QUESTIONS
Businesses are constantly at risk of theft, particularly when their physical assets aren't fully secure. The best way to keep thieves at bay is to break down security into four layers: deterrence, access control, detection and identification.
Physical Layer Security is also concerned with establishing limits of perfectly secure communications, i.e. with zero probability of eavesdropping. A complementary theme is a search for practical techniques which increase the secrecy rates.
The Layer 3 approach to security looks at the entire network as a whole including edge devices (firewalls, routers, web servers, anything with public access), endpoints such as workstations along devices connected to the network including mobile phones to create an effective plan for security management.
Wireless physical layer refers to the layer which protects data to reach reliably from transmitter to the receiver in the presence of noisy channel environment. The channel incorporates various impairments which include fading, phase noise, frequency offset and so on.
While endpoint security is an important component of a strong defense-in-depth posture, the network layer is most critical because it helps eliminate inbound vectors to servers, hosts and other assets while providing an excellent basis of activity monitoring that improves our overall situational awareness.
How Does Layered Security Work?
In the realm of information technology, "layered security" refers to a system of many safeguards designed to prevent unauthorised access to sensitive data.
The idea of tiered security is straightforward. Even if a hacker breaks through one layer of security, the additional layers will keep vital information safe.
This makes it more difficult for hackers to launch an effective cyber attack. The use of multiple layers of defence allows for greater resilience against attacks.
This security method is reminiscent of those seen in classic "heist" films, in which a group of burglars faces increasing difficulty as they attempt to steal a costly diamond and must overcome each new impediment in their path. Locking the exterior doors and windows could be the first line of defence.
If, despite this initial line of defence, an intruder still manages to enter the building, the second line of defence would consist of intrusion detection devices such as alarms on any and all doors and windows.
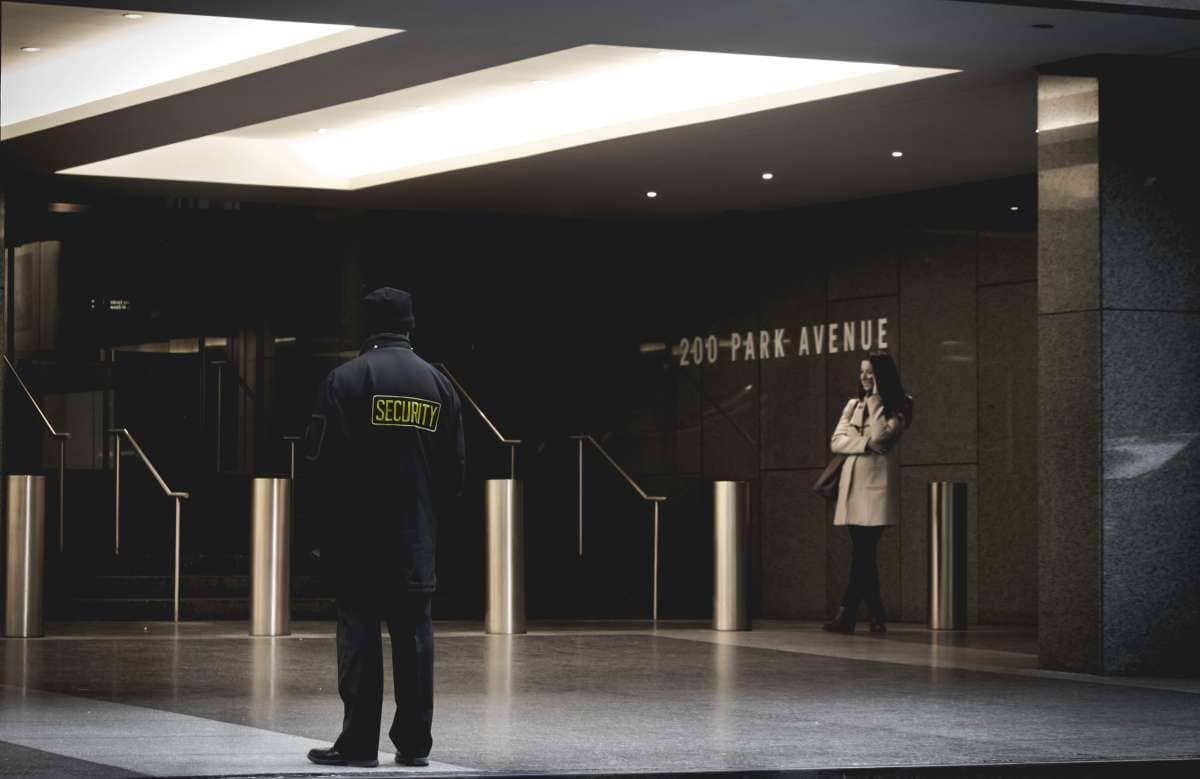
In addition to the security provided by the cameras, the presence of guards within the building adds another layer of protection.
In addition, within movies, ritzy laser beam detectors encircle the case containing the gems, and the motion sensor that sounds an alert if the valuables are removed from their location serves as the ultimate barrier to entry.
The thieves won't be able to claim the diamonds until they break through not just one, but all of the numerous security barriers.
Defense in depth, a military strategy with which the term is synonymous, is another name for layered security. It's common practise for armies to concentrate their soldiers along the front line during battle.
If the attacker concentrates its efforts and breaches thru the display in one place, the area behind will be unprotected.
Some of your troops, fortifications, and weaponry will be stationed further back if you employ a defense-in-depth strategy.
If the front were to be broken through, you still have the resources to counterattack.
In a military setting, even if the adversary is able to achieve an initial breach because there is less concentration in the first level, they can be prevented more quickly since their casualties will continue to mount as they attempt to work their way towards the goal.
The "concentric castle" idea is another well-known use of defence in depth. It is common for a castle's defences to consist of an outside wall, a moat, and an inner wall that is both higher and much more heavily defended.
Layered security provides built-in redundancy in a networked computing environment. There are multiple safeguards in place to ensure that the system as well as its information remain safe even if one fails.
A threat would need to penetrate every layer of protection to have access to the information. There are three primary security controls in a layered security architecture.
Controls For Safety That Build-In Layers
Information security encompasses three distinct areas: governmental, physical, and technical safeguards. Different layers of defence can be implemented for each area of concern.
Regulatory Mechanisms
A company's administrative controls are the policies and processes it has established to lessen its susceptibility to attack and to stop employees from gaining unauthorised access to sensitive data. Layers of standard operating procedures could consist of:
- By instituting a process to deactivate an individual's account on the system, they make sure that only active employees have access to the system.
- They were making elaborate plans to make sure all workers followed the rules when it came to protecting business and charitable information.
- They were implementing a system of role-based access control to ensure that workers could see just the information they required to complete their tasks.
- Privileged accounts, such as administrator accounts, are being used less frequently and are subject to tighter controls.
Regulations Based On Matter
One further important part of the layered strategy is the use of physical controls. Things that prohibit real physiological access to the computer systems are included here. Take, as an illustration:
- All areas containing computers should have actual, locked doors.
- Access to and authentication via computer systems is controlled by fingerprint scanners.
- Security cameras can prevent criminals and detect intrusion attempts online.
- Guards are keeping an eye on things.
- Locked gates to restrict entrance to the area.
As in the aforementioned heist film, numerous layers of physical protections may be in place to prevent thieves from obtaining access to the gems.
Measurements And Controls
Control activities for network security, typically the most complicated of the controls, is another security method required for complete protection.
Information security solutions, both software- and hardware-based, are included in these safeguards to stop unauthorised users from accessing the network and its data.
Different combinations of hardware and software offer the best defence against cyber attacks. The evolving nature of cyber risks makes it imperative that organisations implement numerous levels of technical controls. Possible technological controls include the following layers:
Obtaining Permission
- Strong passwords that can't be easily guessed or broken by password cracking software were mandated.
- Two-factor authentication (2FA) or multi-factor authentication (MFA) is a method of authenticating a user's credentials that requires them to use data from more than one source.
- Authentication based on a user's biometric characteristics, such as their face or fingerprints.
Security Against Malware And Related Attacks
- The first line of defence might come from the administration, in the form of warnings and instructions to users about how to spot and avoid malicious websites and email attachments.
- Anti-virus and anti-malware programmes that rely on signature-based detection could be the next level of defence.
- If a user does accidentally visit a malicious website, Remote Browser Isolation will keep the infection from spreading to the endpoint computer.
Data Privacy And Integrity
- They are using a firewall to protect the network, which can be either a hardware and/or software solution.
- In order to safeguard information in the event that a malicious actor gains access to a server, try encrypting it.
- Adding an extra degree of security by encrypting emails reduces the likelihood of sensitive data being intercepted and used inappropriately by a third party while in transit.
- An extra line of defence that closes an often exploited vulnerability is to use best practises for remote access.
To prevent compromise, it's best to employ many solutions for each category of control. This creates a tiered security architecture that's far more difficult to penetrate.
Businesses must check that the solutions they implement are fully interoperable and can cover their networks without any gaps. Multiple layers of protection should render any potential entry points for hackers irrelevant, protecting the computer and the data it contains.
The Importance Of a Multi-Tiered Strategy For Physical Protection.
It is common knowledge that a multi-layered approach to physical protection is the most foolproof method.
The notion of layered defences is the basis of most security provisions across all types of sites and industries. Imagine the fortifications of a medieval castle, with its many layers of protection for the castle's most valuable possessions.
To begin with, there's the exposed hilltop site, the vast moat, the massive castle walls, and the awkwardly-placed main entryway. This is a great illustration of early physical protection measures. The basic ideas haven't changed much over the years.
This strategy can be thought as a series of layers, each of which delays or deters the physical attack techniques employed by criminals, terrorists, and saboteurs to gain access to places containing crucial or valuable assets.
Purchasing tailored protection that will delay or discourage efforts to physically infiltrate hostile individuals until the first responder arrives is the ultimate investment in time that is needed to ensure adequate physical security.
The cornerstone for enacting workable solutions to safeguard against attempted security vulnerabilities or attacks employing force is the tried and trusted methodology of detecting, delaying, reacting, remediating, and discouraging.
The security, defence, or functioning of the country could all be seriously compromised by an attack of this type.
For such reasons, the National Security Strategy places a high priority on safeguarding both public and commercial sector services from a variety of potential threats.
Threats will increase across the board, impacting everything from water and energy to government and communications.
There must be a concerted effort to find the best solution for each industry and then adopt it.
When protecting a water supply, for instance, it is not enough to simply prevent unauthorised entry; instead, it is also necessary to lock down any exposed assets and any points of entry to ensure that the supply itself cannot be tampered with.
The Eight Essential Safety Measures For Your Data Center
Because of the exponential growth in annual big data production, cloud service providers are increasingly in need of additional storage space brought on by digital transformation. Because of the sensitive nature of the data, applications, and services stored in a data center, companies must take precautions to keep the facility secure.
But what exactly are the safety requirements that your establishment must fulfill and keep up with? Below is how 8-layer security architecture is the gold standard for protecting your information.
Defending The Periphery
The data center's exterior perimeter is protected by a multifaceted wall designed to withstand any form of attack or natural disaster. In order to deter would-be intruders, physical obstacles are crucial..
Stationary Watchtower At The Periphery
The fence's guard post represents the second layer of protection. Visitors should have filled out a registration form at least 48 hours in advance of their visit, answering a series of security questions about their identity, the reason for their visit, and the number of others who will be accompanying them. Once they've been screened and approved, they should only be permitted access to specific zones within the facility.
Place Of Entry
Visitors are required to disclose all things they are carrying and pass through a professional x-ray and metal detector upon admission.
Individual Authorization For Restricted Area
As a next step, guests to the data centre should be issued passes that detail the locations they are permitted to attend as well as those they are not. After entering the "human trap," a small air-locked room, the visitor will be weighed. Security will be alerted if there are noticeable differences between the guests' weights on arrival and departure. This prevents anything from being forgotten that could compromise the facility's security.
Security For Elevator Rides
Visitors to high-rise data centres can proceed directly from the entrance to a lift network access and be limited to using just the elevators assigned to them. For security reasons, only some floors will be accessible to visitors. As long as they have access to the building, everyone there can circumvent the safety measures. To protect the security of the data centre, it is necessary to restrict the amount of time and space that visitors have to move around the building.
Protected Passageway To Data Hall
Installing intelligent devices and CCTV along the aisle will deter tailgating. The Network Operations Center (NOC) must be able to track everyone who enters and leaves the data hall, so enforcing a strict no-tailgating policy is crucial. This is vital since it guarantees that all visitor data is correct, which is necessary in the event of a security breach.
Security Safe For Data Centers
The racks are kept in vaults, so it's important to keep an eye on them and catch any strange behaviour on camera. A cloud infrastructure must always be aware of who is inside the vault and where they are at all times. An alarm should sound if there are any more persons present than expected.
Entry At Rack Level
A biometric key will be issued to a restricted group of individuals only after they have been thoroughly vetted. Data stored on the shelves is protected since biometric passports can't be copied or taken by force. Additionally, many clients might choose to have rack monitoring based on their own requirements.
The best operations staff will plan for the worst situation and implement every available security step to make the building impossible to breach. In this case, it's not enough to just use the accepted norm. The dangerous landscape and technological innovations should be monitored continuously so that facilities can prepare for them.
Conclusion
Security methods are costly, yet their value is sometimes underappreciated. Investing in locks and other similar devices is a cheap way to prevent and delay would-be robbers.
To prevent unauthorised access to private information, a multi-layered security system is employed. Layers of protection provide increased resistance to assault. The initial line of defence may consist of locking all of the external doors and windows.
This hinders the efficiency of any cyber assault that may be launched. Security guards within the building give an extra degree of safety in addition to the cameras outside.
In a distributed computer system, the redundancy provided by many layers of security is invaluable. Both the system and its data are protected by a number of different measures. Any attempt to get access to the data would require the attacker to break through many lines of defence.
Role-based access control, which limits system access to just active personnel, and account deactivation are all possible additions to a set of SOPs. Users might be verified with the aid of biometric data like their faces or fingerprints.
Email encryption lessens the possibility that private information may be intercepted and misused while in transit. By isolating the browser remotely, we can prevent infections from reaching the endpoint machine. The most effective kind of physical security is one that employs many layers of protection at once.
Detecting, delaying, responding, remediating, and deterring attempts at security flaws or assaults using force is a proven and true approach that forms the basis for implementing effective solutions.
There has to be a strict policy in place that only allows visitors to use their designated elevators in the data centres. Any visitors with significantly different weights on check-in and check-out will trigger a security alert. It is critical that the Network Operations Center be able to monitor who enters and exits the data hall.
Content Summary
- All other forms of security are built on top of the basis of physical layer protection.
- Even though they are costly, the value of security mechanisms is sometimes underappreciated.
- It's not always necessary to spend a fortune on expensive metal doors and other such physical security measures.
- The proper handling of paper documents is also crucial for the physical security of a facility.
- Buying a shredder is a simple way to prevent identity theft caused by garbage diving.
- Installing a reliable company security system gives you an advantage over would-be criminals.
- With a reliable physical security system in place, you can rest easy knowing that your property is secure.
- The best defence is a strong offence, and the best offence is a monitoring system that provides many levels of physical security.
- The security system installed in your business should provide you peace of mind, both for its outside and its inside.
- Using several distinct lines of defence increases a system's ability to withstand assaults.
- The first line of defence could be to lock all the doors and windows leading outside.
- Extra security is given by guards stationed throughout the building in addition to the cameras.
- Defense in depth is another name for multilayer security.
- In a defense-in-depth plan, some of your men, fortifications, and weapons will be stationed further back.
- A second well-known example of defence in depth is the "concentric castle" concept.
- In a networked computing system, layers of security offer built-in redundancy.
- When it comes to the security of the system and its data, many backups have been implemented in case one fails.
- A layered security architecture consists of three main security measures.
- There might be many lines of defence set up, one for each potential threat.
- Administrative controls are the procedures and policies put in place by an organisation to prevent data breaches and unauthorised access by personnel.
- Using physical controllers is also an integral aspect of the tiered approach.
- There must be several layers of security in place, with network security control activities being a particularly complex layer.
- To verify their identity, users of two-factor authentication (2FA) or multi-factor authentication (MFA) systems need to provide information from several sources.
- The next line of defence might be antivirus and anti-malware software that uses signature detection.
- A firewall, which might be hardware or software, is being used to secure the network.
- Implementing standard practises for remote access provides an additional layer of defence against an often exploited weakness.
- It is well-known that the most secure technique of physical security is one that consists of many layers of defences.
- Most security measures at all kinds of locations and in all kinds of sectors are based on the idea of layered defences.
- The ultimate expenditure of time required to provide proper physical security is the purchase of customised protection that will delay or discourage efforts to physically infiltrate hostile persons until the first response arrives.
- Everything from the water supply and power grid to government operations and media networks will come under increasing attack.
- With the annual growth rate of big data at an exponential rate, digital transformation has created a pressing demand for cloud service providers to increase their storage capacity.
- Companies must take measures to ensure the safety of their data centres since the information, software, and services they house are extremely valuable and confidential.
- The outside of the data centre is fortified with a multilayered wall that can withstand any kind of attack or natural disaster.
- Visitors to the data centre need to be given passes that specify which areas they have access to and which they do not.
- Any significant fluctuations in guests' reported arrival and departure weights will trigger a security alert.
- Guests of multi-story data centres can bypass the lobby and head straight for the lift network access, where they'll be confined to utilising just the elevators that have been specifically designated for their use.
- Visitors will be restricted to some floors for safety reasons.
- It is important to limit visitors' access to the data centre by both time and space in order to keep the facility secure.
- Installing smart gadgets and CCTV along the aisle will reduce tailgating and provide a safe path to the data hall.
- A stringent no-tailgating policy is essential, as the Network Operations Center (NOC) has to be able to monitor who enters and exits the data hall.
- Keeping a watch on the racks in the vaults and recording any unusual behaviour is essential.
- The most efficient operations teams anticipate the worst and take all reasonable precautions to make their facilities impregnable.