At least this part is easy to understand. Every structure requires some kind of security measure to prevent unauthorised entry. Even if a person has been invited inside an establishment, that organisation probably has a policy that requires them to keep certain parts of the building off-limits to visitors. Because of this, you will need to implement a series of safety precautions to ensure that only authorised personnel, who have been specifically chosen for the privilege of accessing protected amenities, are permitted to use those amenities. Within a manufacturing plant or office space, these security precautions should be implemented after a more comprehensive plan that is designed to safeguard your equipment, resources, and any other assets have been put into place. Your strategy for achieving physical security is comprised of all of these different measures working together.
The most effective and practical methods of achieving safety objectives through physical security make use of various forms of technology and specialised hardware. You will be tasked with the responsibility of guarding your property against trespassers, internal dangers, online assaults, accidental damage, and natural disasters. This will call for a combination of technological and human surveillance, as well as careful planning and the strategic placement of security personnel and other strategies. In order for your preventative measures and defensive measures to be efficient, you also have to implement a security perimeter. The size of this perimeter and the scope of its protection may change depending on the specific requirements of your facility and the potential dangers that may be posed to it. If you want to ensure that your space is secure from a physical standpoint, you need to look at it as a whole rather than breaking it down into its component parts.
Physical Security System Measures
A more all-encompassing approach to security will invariably include elements of physical security, but those elements will make up a sizeable portion of this larger plan. Access control, monitoring, and testing are, according to those who specialise in the field of security, the three most important aspects of a physical security plan. These aspects, which complement one another to make your location more secure,
It's possible to begin controlling access at the most peripheral point of your security perimeter, which is something you should do as soon as possible in this process. You can monitor access to your facility and ensure security in the outdoor area by utilising fencing and video surveillance, particularly if you have on-site carparks or other resources located outside of your building. In addition to using advanced locks, mobile phones, or biometric authentication, access control cards, and authorisation, an all-encompassing access control system and strategy would include the use of mobile phones. The majority of establishments begin the process of controlling entry at the front door, where cardmembers can swipe their one-of-a-kind identification badges or use their mobile phones. From that vantage point, it is possible to instal card readers on virtually any surface, including the doors of offices, conference rooms, and even kitchens. It is not necessary for any employee to clock out because they all leave using the same procedure; therefore, there is no need to check to see if anyone is inside the facility after closing time.
Another important aspect of your space that you should think about incorporating is surveillance. In today's modern security systems, multiple sensors, such as those that detect motion, heat, and smoke, can be utilised to provide protection not only from criminal activity but also from accidental fires and explosions. These sensors can establish a direct connection to your security system, which enables them to activate alarms and notify you and any other system administrators without requiring any intervention from a human being. It stands to reason that the implementation of surveillance cameras and alarm systems should also be a part of your overall security strategy. These technologies can record the illegal activity and make it much easier to track down those responsible. You are able to monitor the system from your mobile console with cloud-based access control solutions because these solutions automatically update themselves over the air as well as provide real-time reports.
When a disaster occurs, you need to respond quickly and carry out the protocols that you have established. Because of this, it is imperative that you perform routine tests of your disaster recovery plan, both on the technological level and the human level. Exercises should test your ability to respond in an emergency situation involving a natural disaster or an emergency caused by an internal or external threat that poses a risk to personal safety or data. In the event that an emergency occurs that requires the evacuation of your building, thankfully, access control systems give you the ability to determine who is still inside the building and who has already left. You need to make sure that there are no weak points when it comes to access to essential business resources such as server rooms, production lines, data centres, power equipment, and anything else that could have an effect on your day-to-day operations. If you are going to be furnishing a sensitive location, like a school or a place of worship, you should probably think about getting a security system that has a lockdown function.
How Does Physical Security Work?
Physical security measures are critical to safeguarding personnel, hardware, software, networks, and data from various threats such as burglary, theft, vandalism, terrorism, fire, flood, and natural disasters. While insurance can cover most risks, prioritizing damage prevention through physical security measures can prevent loss of time, money, and resources.
Access Control
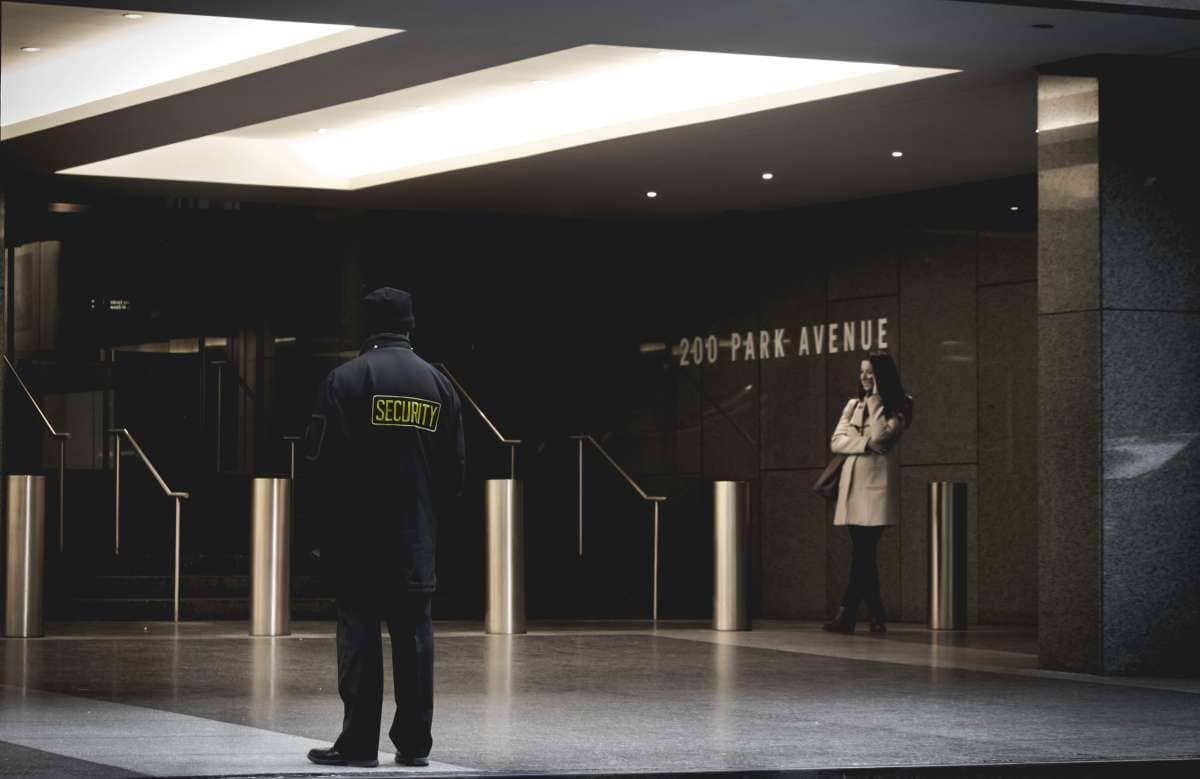
Access control is an effective way to maximize physical security measures by restricting and controlling entry into specific areas and materials. Identification badges, keypads, and security guards are common examples of access control barriers. Physical barriers like fences, gates, walls, and doors serve as the first line of defense for most physical security systems.
Sophisticated access controls employ technology-supported approaches such as ID card scanners and near-field communication (NFC) ID cards. Obstacles strategically placed in the path of attackers can also make it more difficult for them to gain access to valuable assets and information.
Surveillance
Surveillance is an essential aspect of physical security, used to monitor activities in various locations and facilities. Closed-circuit television (CCTV) cameras capable of recording activities in multiple locations at once are the most common form of surveillance. Surveillance plays a role in both preventing incidents and responding to them.
Testing
Testing physical security measures is becoming an increasingly essential practice to ensure the cohesiveness of an organization's disaster recovery plans. Regular policy tests should be conducted to rehearse role assignments and responsibilities, thereby reducing the likelihood of errors occurring.
By implementing physical security measures such as access control, surveillance, and testing, organizations, agencies, and institutions can safeguard against threats and prevent the loss of time, money, and resources.
Why Physical Security Is Important
At its most fundamental level, physical security entails protecting your buildings, people, and property from dangers that are based in the real world. It includes both the detection of intruders and the taking of action in response to the threats that have been identified.
Although it could be the result of environmental occurrences, the term is more commonly used to refer to the process of preventing individuals, whether they be external actors or prospective insider threats, from gaining access to areas or assets that they are not authorised to use. It could mean preventing members of the general public from entering your headquarters, preventing on-site third parties from entering areas where sensitive work is performed, or preventing employees from entering mission-critical places such as the main server.
An example of a physical attack would be getting into a restricted area of a building, breaking into a secure data centre, or using terminals that the perpetrators have no right to access. Theft or damage of important IT assets, such as servers or storage media, gaining access to virtual stations for mission-critical apps, stealing information via USB, or uploading malware onto your systems are all possibilities when an attacker is present.
It is expected that stringent controls at the very edge of the perimeter will be able to ward off any outside dangers. At the same time, internal security measures should make it less likely that there will be attackers from within the organisation.
It is possible that smoking areas, entrances to on-site gyms and even loading bays will not be guarded, monitored, or secured in any way. Turnstiles and other similar barriers that have motion sensors on the exits can also be easily opened by placing a hand through to the other side and waving it all around. This will allow the person on the other side to pass through.
While the cost of successfully launching a digital attack continues to rise, the cost of suffering physical damage to your investments can be just as detrimental. One of the most infamous examples of a breach in physical security.
Benefits Of Physical Security Measures
The technology and devices that you choose may include additional features that can enhance the safety of your workplace. This is in addition to the obvious benefit that physical security systems provide, which is to protect your building. You will have increased flexibility to manage your system remotely, in particular if it is cloud-based physical security control, and you will also be able to connect with other building control and protection systems.
- Secure the building and make sure no one can get in without permission. Nearly a third of employees report feeling unsafe on the job, which can have negative effects on both output and morale. Customers' safety should be a top priority. Customers need to know that their information is safe with you, and that their privacy is respected. A breach of sensitive information can destroy the reputation your company has worked hard to build. To protect your property, assets, and employees from harm and loss, implement a stringent access control as part of your physical security plans.
- Anticipatory detection of intrusion - Physical security measures are your first and best line of defence against unwanted visitors. By installing a top-tier access control system, you can keep track of who enters and exits your building at any given time. With Openpath, an easy-to-install system, your intrusion prevention system will be up and running in no time. Furthermore, the cloud-based software allows you to view real-time activity from any location and receive entry alerts for various physical security threats such as a forced entry, an unauthorised entry attempt, and more. You can take care of emergencies more quickly and easily thanks to Open Path's lockdown feature, which allows you to remotely trigger a complete lockdown of the system. More preventative security measures for your office workstation can be found in cloud-based and cellphone access control systems.
- Data stored in the cloud eliminates the need for expensive and easily exploitable onsite servers and hardware. This allows for a more scalable implementation of physical security. Cloud-based physical security control can be seamlessly integrated with your current infrastructure and applications. A scalable solution that is simple to instal and quick to set up will make upgrading to a new physical security system much less of a hassle for businesses of all sizes, especially those experiencing rapid expansion. When compared to older, more rigid systems, cloud-based ones make it simpler to make changes like adding or removing users, switching to a new piece of hardware, or rolling out the system to multiple buildings.
- Another perk of cloud-based physical security systems is their ability to seamlessly integrate with existing systems. A strong physical security plan must include a reliable access control system, but that plan is further fortified by the integration of additional security measures. Openpath's access control is just one example of a product that can be easily integrated with other business-critical software thanks to its open application programming interface (API).
- One advantage of security control systems is that the supplementary detection methods typically include reporting and audit of the activity in your building. This information is vital to your safety. If you can quickly and easily identify potential points of failure in your system, you can adjust your physical security measures accordingly. If a breach does occur, having thorough records will help law enforcement catch the perpetrator and put an end to the breach as soon as possible. To reduce the workload on HR and IT, you can use analytics to track how well your physical security measures are working.
Physical Security Measures Every Organisation Should Take
Security For Your Doors
Do you have secure doors on your server room? The door to the server room needs to have sturdy locks installed. It is important to verify a few conditions before proceeding with server room security.
- Ideally, there would be minimal lighting in the space. Don't put up signs that give away the contents of the room. "Confidential, sensitive, and expensive equipment here," for instance.
- There shouldn't be a lot of windows in the room, but there should be high walls and a fireproof ceiling.
- Only authorised personnel should be granted entry to the area and its associated physical networks. All locks should be changed if there is a security breach.
- Window bars, anti-theft wiring, motion detectors, and magnetic vital cards are just a few of the alternatives you can use to deter theft.
Monitoring And Surveillance
Has the personnel in charge of physical security been taught how to keep a logbook? Maintaining a current roster of all security personnel with appropriate clearances is essential. Never let anyone move or service your equipment without permission. The service provider must show a photo ID or the original work order when requested. Keep records of everything that happens like this.
The adoption of stringent locking procedures for the server room is also an important first step. Yet, security could still be breached, or those with legitimate access could abuse their position. Smart cards, tokens, or biometric scans can be installed as part of a comprehensive access control system that logs the identities of all building visitors. Additionally, video door surveillance cameras and motion detection technology can be useful for keeping an eye on things.
Keep The Network Devices In The Secured Room
It is not just the servers that need to be guarded. Hackers can gain access to sensitive information by connecting a laptop to the wireless network's access point and then capturing data in plaintext using packet analysis or sniffer software. Anything that can connect to that network should be kept in the same secure location. You should store them safely in a locked closet if you have to keep them in separate locations.
Conclusion
Security measures include a perimeter wall, guards stationed in strategic locations, and monitoring equipment. The three most crucial elements are access management, monitoring, and testing. Advanced locks, mobile phones, biometric authentication, access control cards, authorisation, and surveillance cameras and alarm systems should be used to regulate entry at the outermost points of your security perimeter. Protection against break-ins, theft, vandalism, terrorism, fire, flood, and natural disasters are just some of the many reasons why physical security measures are so important. Access control, surveillance, and testing are all examples of physical security measures that are crucial in protecting businesses, government agencies, and educational institutions from potential harm and the associated waste of time, money, and materials.
Safety and the ability to manage and connect to other systems can both benefit from physical security measures. Protect the building's assets, employees, and visitors from harm by enforcing strict access control as part of your physical security plan. Upgrading to a new physical security system is made much less difficult by cloud-based systems because they are simple to install and integrate with existing systems.
Content Summary
- Every structure requires some kind of security measure to prevent unauthorised entry.
- Because of this, you will need to implement a series of safety precautions to ensure that only authorised personnel, who have been specifically chosen for the privilege of accessing protected amenities, are permitted to use those amenities.
- Your strategy for achieving physical security is comprised of all of these different measures working together.
- In order for your preventative measures and defensive measures to be efficient, you also have to implement a security perimeter.
- If you want to ensure that your space is secure from a physical standpoint, you need to look at it as a whole rather than breaking it down into its component parts.
- Access control, monitoring, and testing are, according to those who specialise in the field of security, the three most important aspects of a physical security plan.
- These aspects, which complement one another to make your location more secure,
- It's possible to begin controlling access at the most peripheral point of your security perimeter, which is something you should do as soon as possible in this process.
- You can monitor access to your facility and ensure security in the outdoor area by utilising fencing and video surveillance, particularly if you have on-site carparks or other resources located outside of your building.
- In addition to using advanced locks, mobile phones, biometric authentication, access control cards, and authorisation, an all-encompassing access control system and strategy would include the use of mobile phones.
- Another important aspect of your space that you should think about incorporating is surveillance.
- It stands to reason that the implementation of surveillance cameras and alarm systems should also be a part of your overall security strategy.
- You are able to monitor the system from your mobile console with cloud-based access control solutions because these solutions automatically update themselves over the air as well as provide real-time reports.
- Because of this, it is imperative that you perform routine tests of your disaster recovery plan, both on the technological level and the human level.
- Access control is an effective way to maximize physical security measures by restricting and controlling entry into specific areas and materials.
- Identification badges, keypads, and security guards are common examples of access control barriers.
- Physical barriers like fences, gates, walls, and doors serve as the first line of defense for most physical security systems.
- Surveillance is an essential aspect of physical security, used to monitor activities in various locations and facilities.
- Testing physical security measures is becoming an increasingly essential practice to ensure the cohesiveness of an organization's disaster recovery plans.
- By implementing physical security measures such as access control, surveillance, and testing, organizations, agencies, and institutions can safeguard against threats and prevent the loss of time, money, and resources.
- At its most fundamental level, physical security entails protecting your buildings, people, and property from dangers that are based in the real world.
- It includes both the detection of intruders and the taking of action in response to the threats that have been identified.
- It is expected that stringent controls at the very edge of the perimeter will be able to ward off any outside dangers.
- At the same time, internal security measures should make it less likely that there will be attackers from within the organisation.
- Turnstiles and other similar barriers that have motion sensors on the exits can also be easily opened by placing a hand through to the other side and waving it all around.
- This will allow the person on the other side to pass through.
- While the cost of successfully launching a digital attack continues to rise, the cost of suffering physical damage to your investments can be just as detrimental.
- One of the most infamous examples of a breach in physical security.
- The technology and devices that you choose may include additional features that can enhance the safety of your workplace.
- This is in addition to the obvious benefit that physical security systems provide, which is to protect your building.
- You will have increased flexibility to manage your system remotely, in particular, if it is cloud-based physical security control, and you will also be able to connect with other building control and protection systems.
- To protect your property, assets, and employees from harm and loss, implement stringent access control as part of your physical security plans.
- Anticipatory detection of intrusion - Physical security measures is your first and best line of defence against unwanted visitors.
- By installing a top-tier access control system, you can keep track of who enters and exits your building at any given time.
- An easy-to-install system, your intrusion prevention system will be up and running in no time.
- More preventative security measures for your office workstation can be found in cloud-based and cellphone access control systems.
- This allows for a more scalable implementation of physical security.
- Cloud-based physical security control can be seamlessly integrated with your current infrastructure and applications.
- A strong physical security plan must include a reliable access control system, but that plan is further fortified by the integration of additional security measures.
FAQs About Security Monitoring
Design, control, detection, and identification are the four fundamental tiers of physical security. There are various security choices that can be used for each of these stages. Any structure that can be erected or installed to prevent attacks is referred to as having a physical security design.
A security control is any precaution or preventative mechanism intended to avoid, identify, mitigate, or reduce security risks to real estate, data, computer systems, or other assets. Data security controls are more crucial than ever now because of the increase in cyberattacks.
Security countermeasures can be categorised into the following categories based on how they are functionally used: preventive, detective, deterrent, corrective, recovery, and compensating.
Common controls can be any kind of security measure or safeguard that keeps your information system's confidentiality, integrity, and availability in check. As contrast to the security controls you choose and create yourself, these are the security controls you inherit.
Internationally recognised CIS benchmarks serve as security guidelines for protecting data and IT systems against threats. They provide prescriptive instructions for creating a secure baseline configuration and are employed by thousands of enterprises.