Organizations that take the security of their online presence seriously will set up some sort of continuous monitoring system. According to NIST, continuous monitoring is the practise of keeping an organisation aware of information security, vulnerabilities, and threats in order to guide risk management decisions. This method allows for continuous monitoring of a company's risk factors and cybersecurity performance in real time. What was once an insurmountable task is now easily achievable with the help of automatic data collection techniques.
Effective cybersecurity programmes require in-depth familiarity with a company's risk profile, existing IT infrastructure, organisational alignment, responsibility, and support, as well as dependable management and enterprise visibility into risk. Some of the ways in which a business could profit from and actively promote a 24/7 monitoring programme are outlined below.
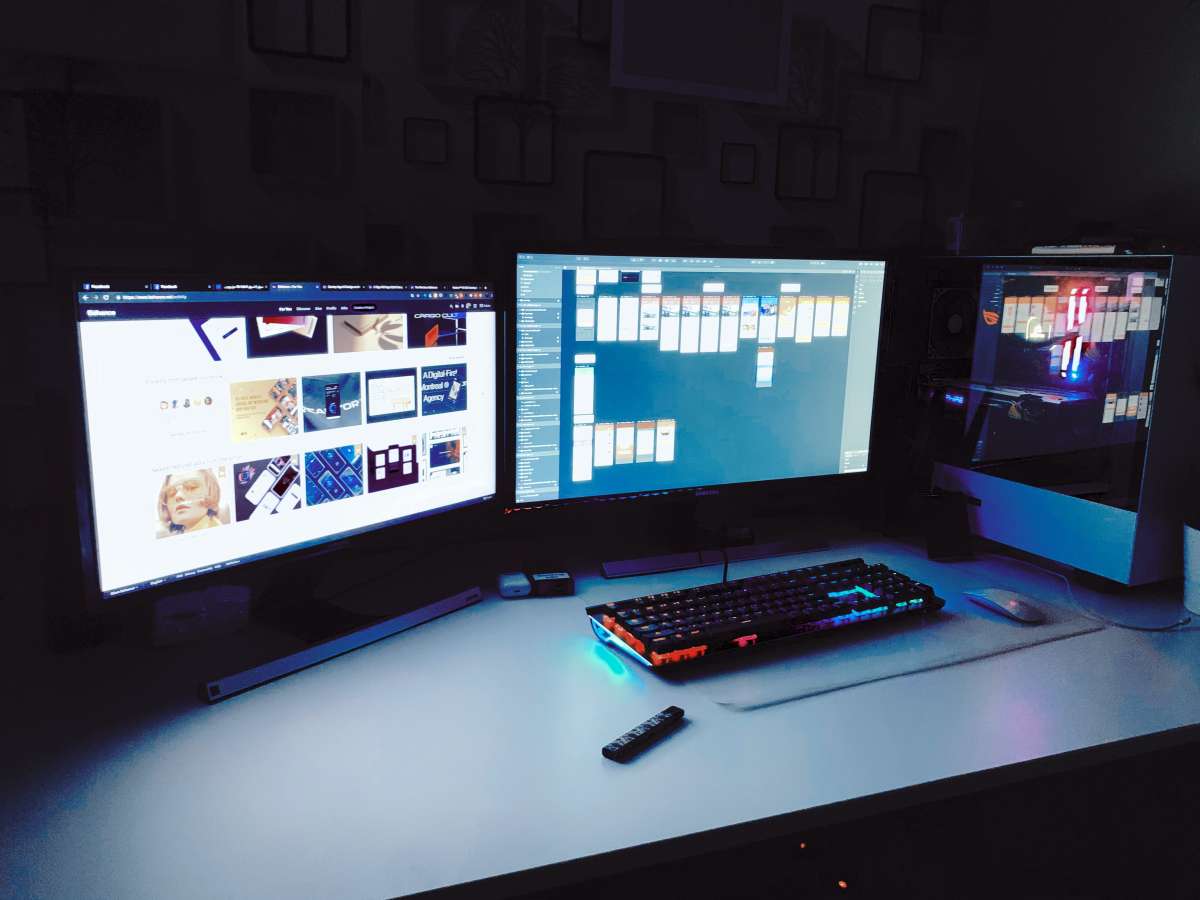
A continuous monitor is a type of display that is typically kept on a desk and can be of any size. Some units "sit" on the bench, while others are secured to the matting of the working surface or even attached beneath the workbench to save desk space. By linking to the operator's wrist straps, the equipment enables continuous real-time monitoring. If the wrist strap fails, the team will sound an alarm. Many continuous monitors have a parking snap that snaps the screen off when the user walks away from their desk.
Categories of Real-Time Displays
The two primary varieties of continuous monitoring equipment are:
- Any standard single-wire coiled cord or wrist strap can be utilised with a continuous single-wire monitor. Monitor/wrist strap systems have much lower life-cycle costs than dual-wire systems.
- While not recommended for critical applications, single-wire continuous monitors can be used to keep an eye on both the operator's wrist strap and the workstation surface at a fraction of the cost of more expensive options.
- Dual-wire continuous monitors are effective in keeping tabs on the wrist strap's performance and the operator's wellbeing at all times. If the operator is using a dual-wire continuous monitor, and one of the wires in the wrist strap were to be severed, the other would still provide a safe path to ground. To implement dual-wire technology, coiled cords and wrist straps must incorporate two separate sets of wires.
The Value of Constantly Monitoring Systems
Condition of the Device
Having a comprehensive knowledge of the infrastructure components that are directly managed by the organisation is a huge advantage of a monitoring programme that runs 24/7. Success in the future hinges on your familiarity with your digital footprint. It can be used for figuring out what to do with old systems, cutting down on entry points for attackers, or determining which assets are most important. For these and other reasons, it's crucial to be aware of your field equipment. Using this information can cut down on expenses, lessen risk, streamline processes, and boost productivity.
Global Threats and the Current Environment
Having a thorough understanding of the systems that make up your ecosystem is only half the battle; in order to fully grasp the foundations of the actual risk provided by certain strategies, threat profiles must be developed for all business systems. In order to allocate security resources effectively, it is essential to conduct a risk assessment of all mission-critical systems within a company's digital ecosystem and focus on those with the highest potential for financial damage in the case of a cyberattack. As a result of this deeper insight, it is much simpler to recognise vulnerable systems that fraudsters may attempt to breach. With this knowledge in hand, security resources can be better prioritised, resulting in the greatest possible marginal reduction in organisational risk.
Capability to Monitor Cybersecurity Metrics
In addition to preventing security breaches, another perk of constant monitoring is that it allows you to monitor critical cybersecurity performance indicators (KPIs). Organizational data can be aggregated with the use of automated systems, allowing for more accurate tracking of a wider range of business KPIs. These cybersecurity performance indicators can be used for a wide variety of purposes, including but not limited to locating security holes, monitoring the efficiency of controls, associating financial resources with specific security enhancements, promoting accountability, and guiding governance. If these KPIs are monitored, it will be feasible to create a security plan that is both cost-effective and comprehensive.
The Ability to Make Choices with Greater Deliberation
Conducting thorough market research and making informed judgments in response to market conditions are two of the most important parts of running a successful business. Having up-to-date and accurate information at hand is crucial when making business decisions. That's why it's important to implement a continuous monitoring programme that gives key decision-makers the data they need to understand the state of their digital environment at all times. With this information at their disposal, companies can swiftly respond to shifting market conditions and seize emerging possibilities.
It takes time to set up a reliable system of constant monitoring. Planning, work, time, and a dedicated group, with executive buy-in, are essential. There is, however, cause for optimism: there are sources, tools, and frameworks available to assist businesses get off to a fast start when it matters most. Accurate and thorough understanding of the digital ecosystem, current cybersecurity measures, and future cybersecurity goals of the firm is one of the most important factors in developing an effective cybersecurity programme. The ability to effectively identify organisational systems' strengths and flaws is priceless. When businesses have a system in place for constant monitoring, they are better equipped to determine where their resources are needed to achieve the greatest gains in observable performance.
Rapid Response
Let's say you come into work each day, test your wrist strap to make sure it won't cause an ESD event, and then get to work on your ESD-sensitive gadgets. You take a three-hour tea break, during which time you examine your wrist strap and find that it is now defective. I don't know what to do. Whether the wrist strap failed just now or right after your first exam this morning is unknown to you. How can you tell if the gadgets you spent the morning fixing are still functional? After all, hidden flaws are impossible to spot, and errors might not manifest themselves until much later. As soon as the wrist strap fails, the operator will be notified that they are working with ESD-sensitive electronics. No ESD-sensitive gadgets will be harmed, and no consumers will be dissatisfied if the defective wrist strap is swapped out for a working one from stock.
Keep an Eye on The Operator And The Machine.
Surface ground connection monitoring is an optional feature of most continuous or constant monitors. "The grounding of work surfaces is something that can be tracked by certain constant monitors. A signal is sent through the ground and work surface connections to check their integrity. The alarm goes off if the resistance suddenly drops or increases beyond a preset threshold. Work An electrical connection between the surface monitor, the desk, and the ground is verified by a surface monitor. However, insulative pollution on the desk will go undetected by the monitor." Survey of Constant (Continuous) Wrist Strap Monitors [ESD TR 12-01 Technical Report]
What determines how much current flows when a monitor is attached to an ESD Mat work surface is the overall resistance between the monitor and the working surface. Monitor will show good when the resistance of the work surface is less than a user-defined threshold*. On the other hand, the monitor will sound an alarm if the resistance value is significantly higher than the reference value. This metering circuit integrates the resistance being measured. Consequently, it is resistant to electromagnetic fields generated by sources outside of itself.
The Detection of Early Flex Fatigue
Continuous monitors are preferable to wrist strap testers because they can identify problems during the wrist strap's "intermittent" phase of operation. This is being done in preparation for a permanent "open," which poses a threat to components sensitive to electrostatic discharge. You Won't Need to See Your Doctor As Often
Continuous monitoring is replacing periodic touch testing of wrist straps as the prefered method of assuring customers that their products were manufactured in an ESD-safe environment. Continuous monitors eliminate the need for users to test and log the results of wrist straps in accordance with the EN 61340-5-1 test recording standards as a result of their design.
So when using constant monitoring, operators:
- Before each shift, you won't have to waste time waiting in line for a wrist strap test.
- They are relieved of the burden of keeping up with daily test logs.
If you're being constantly monitored, it's far more difficult to cheat. We're not implying that your staff is dishonest, but we have witnessed things like operators "pretending" to check their wrist straps, operators failing a wrist strap test but still registering a pass, etc. Constant monitoring makes it more difficult to circumvent a system, but it's never impossible.
Should you immediately go out and buy constant monitors for all of your users in light of this new information? Like so many things in life, the answer is not black or white; rather, it depends. If your company manufactures products with ESD-sensitive components, you should ask, "How critical is the reliability of our products?" Because eventually, every wrist strap will break. Products of this magnitude require a system of constant monitoring to guarantee that all workers are present and accounted for at all times.
Non-Compliance Benefits of Constantly Checking Systems
We showed how a digital, real-time temperature monitoring system is far superior to a manual, clipboard-based one. We have a lot better shot at keeping up with the ever-evolving compliance rules.
This article explores five areas where compliance-based monitoring falls short and how continuous monitoring can help.
Reduced Potential Danger
A digital system will allow managers to be alerted instantly if a temperature excursion happens at any given pharmacy inside a big retail chain, allowing them to take corrective action before any serious violations occur. A company's reputation and the public's trust can be damaged by negative press surrounding the improper handling of pharmaceuticals or vaccines. The costs of not switching to a digital system, such as replacing lost or stolen medications, paying regulatory fines, settling lawsuits, or vaccinating children again, are much higher than the costs of making the switch.
Securing Financial Resources
The loss of thousands of dollars' worth of medicine because of a malfunctioning refrigerator is commonplace in the pharmacy industry. Most pharmacies protect themselves from financial catastrophe by enrolling in insurance policies. Monitoring temperatures constantly to see if temperature-sensitive medicines have been compromised is still not something many people do. Not only do insurance plans frequently fall short when it comes to covering expensive medications like chemotherapy, immunosuppressants, injectables for chronic conditions (like insulin for diabetes), and biologics, but they also have trouble covering large quantities of temporary stock like flu vaccines. Therefore, it is critical to protect assets by installing a system that can monitor temperatures round-the-clock.
Getting the Most Out of What We Have
If you're trying to maximise profits in an era of tighter margins, investing in a digital system will help you do just that, by optimising your use of human capital. Innovative temperature monitoring systems can increase earnings by freeing up staff time for patient care. Why employees waste time conducting manual temperature checks when automated systems are readily available begs the question.
Keeping Promises
Pharmacies owe their customers ethical and moral care in the form of competent service. Maintaining best practises that ensure patients' safety and health requires strict adherence to all relevant temperature laws and regulations, and even more so than is required.
Enhancing Worth
Maybe you're still not convinced that the value of data that's available 24/7 justifies the cost of a digital system. Should temperatures really be taken each 5-15 mins? In addition to the benefits I just listed, the following is the solution: the data collected from your organization's activity logs can be used to improve many facets of its operations.
Our system's analytics will remind you when it's time to service the refrigeration units. Temperature readings, when used in conjunction with information about the compressor's cycling, can predict when a specific unit will fail, allowing for timely preventative maintenance to be scheduled. Furthermore, you can determine with greater precision which pieces of machinery need to be replaced quickly, thus allowing you to spend only on absolutely necessary capital purchases during the current fiscal year.
When the equipment's make as well as model are recorded alongside the readings & time stamps, the information can be used to make a comparison, providing useful insight into which products are best when shopping for replacements.
Taking Advantage of Cloud-Based, Real-Time Compliance Monitoring
Risk Management for the Cloud
In 2017, cloud service providers like Amazon Web Services (AWS) released additional data storage options and processing capabilities, ushering in the next generation of cloud computing. Organizations must manage cloud services that employees use but which are not directly governed by the IT department in order to reduce the security and privacy concerns that are inherent to their use.
Constant Monitoring is of Paramount Importance.
By monitoring data in real time, managers may see how their cybersecurity and privacy measures are doing at any given moment. All sizes and types of businesses can benefit from the following supervisory tasks:
- Constant internal testing
- Verification of the cloud's security on a continuous basis from the outside
- Constant refinement
- Management of the supply chain that is always on.
The Value of Constantly Checking in
Executives and those in charge of allocating company resources will appreciate hearing about some significant advantages of a continuous monitoring programme.
- Information security, privacy, and compliance risk monitoring in real time.
- Authorization of standard controls and information systems for continuing operations, supported by institutionalised mechanisms for real-time monitoring.
- Giving top-level management the data they need to minimise wasted time and resources on risk assessment and mitigation.
- Complete data, application, and system development life cycle integration of information security and privacy controls and protections.
- Organizational risk management is supported by data, applications, and systems that are linked to and integrated with enterprise-level risk management procedures.
- Having confidence in those who take charge of controls and risk management activities and holding them accountable for their actions.
Dangers to Supply-Chain Security
Vendors, third parties, and business partners often create security issues and privacy leaks. Reviewing all of your cloud service's vendors, suppliers, contractors, and other third parties regularly is crucial for keeping your data safe in the cloud.
To start, businesses need to identify which external entities are mission-critical and have access to sensitive information.
Connecting Dots
Careful preparation is required to effectively manage the myriad of cloud-based security risks. Professionals in the field of information assurance can better protect organisations against the dangers posed by cutting-edge technology and methods by engaging in constant surveillance. All of our regular processes need to include security checks.
Companies in every industry throughout the world are facing unprecedented threats to their data's integrity, privacy, and legality. The use of cloud computing brings with it a number of difficulties, many of which are associated with the use of cutting-edge, novel methods and tools. Services and goods in the supply chain are increasingly being delivered over the internet or stored on remote computers, raising the need to safeguard against threats posed by the cloud.
Pros in the field of information assurance can lessen the impact of potential threats by keeping a close eye on things 24/7. Put on your professional security hat and get the open backing of executive management; put in place the means of constant monitoring and oversight; make legal compliance the standard; and keep a close eye on your suppliers and the products they produce. Keep one step ahead of cybercriminals and auditors when your business's central model shifts to the inevitability of the cloud.
Conclusion
Information security, vulnerabilities, and threats can all be monitored on a continuous basis. In this way, the state of a company's cybersecurity and its exposure to potential threats can be tracked in real time. In this article, we'll go over some of the ways a company can take advantage of and actively promote a 24/7 monitoring programme. Saving money, lowering risk, streamlining operations, and increasing output are all possible with its help. When this information is at hand, security resources can be better prioritised, resulting in the greatest possible marginal reduction in risk.
Making educated business decisions requires access to timely and accurate data. The data-driven decisions of an organisation depend on the results of a continuous monitoring programme. When businesses have the ability to adapt quickly, they can seize new opportunities as they arise. Certain constant monitors can be used to keep an eye on work surfaces. If the resistance suddenly decreases or increases by more than a certain amount, an alarm will sound.
Users no longer have to conduct tests on their own wrist straps and record the results in accordance with EN 61340-5-1 test recording standards if they use a continuous monitor. A manual system based on a clipboard can't compare to a digital, real-time system for tracking temperatures. Still, few people routinely check the temperature of their refrigerators to see if their temperature-sensitive medications have been compromised. Switching to a digital system will save money in the long run, but only if you do it. Customers have a moral and ethical expectation that pharmacies will provide them with competent service.
Compliance with all applicable temperature laws and regulations is essential to maintaining best practises that protect patients' health and safety. Earnings can be boosted by allowing more time for patient care thanks to modern temperature monitoring systems. Continuous risk assessment for data privacy, security, and regulatory compliance. Integrating enterprise-level risk management processes with data, applications, and systems. It is critical to regularly review all of the vendors, suppliers, contractors, and other third parties associated with your cloud service.
There are a few problems with cloud computing, and many of them stem from the fact that it makes use of innovative, cutting-edge techniques and software. Experts in the field of information assurance are able to mitigate the effects of security risks by monitoring systems around the clock.
Content Summary
- This method allows for continuous monitoring of a company's risk factors and cybersecurity performance in real time.
- Having a comprehensive knowledge of the infrastructure components that are directly managed by the organisation is a huge advantage of a monitoring programme that runs 24/7.
- Success in the future hinges on your familiarity with your digital footprint.
- In order to allocate security resources effectively, it is essential to conduct a risk assessment of all mission-critical systems within a company's digital ecosystem and focus on those with the highest potential for financial damage in the case of a cyberattack.
- In addition to preventing security breaches, another perk of constant monitoring is that it allows you to monitor critical cybersecurity performance indicators (KPIs).
- It takes time to set up a reliable system of constant monitoring.
- Surface ground connection monitoring is an optional feature of most continuous or constant monitors. "
- Work An electrical connection between the surface monitor, the desk, and the ground is verified by a surface monitor.
- We showed how a digital, real-time temperature monitoring system is far superior to a manual, clipboard-based one.
- This article explores five areas where compliance-based monitoring falls short and how continuous monitoring can help.
- Innovative temperature monitoring systems can increase earnings by freeing up staff time for patient care.
- In addition to the benefits I just listed, the following is the solution: the data collected from your organization's activity logs can be used to improve many facets of its operations.
- Constant internal testing Verification of the cloud's security on a continuous basis from the outside Constant refinement Management of the supply chain that is always on.
- Executives and those in charge of allocating company resources will appreciate hearing about some significant advantages of a continuous monitoring programme.
- Reviewing all of your cloud service's vendors, suppliers, contractors, and other third parties regularly is crucial for keeping your data safe in the cloud.
- Professionals in the field of information assurance can better protect organisations against the dangers posed by cutting-edge technology and methods by engaging in constant surveillance.
- The use of cloud computing brings with it a number of difficulties, many of which are associated with the use of cutting-edge, novel methods and tools.
- Pros in the field of information assurance can lessen the impact of potential threats by keeping a close eye on things 24/7.